XP can’t connect via vSphere 5.5 client
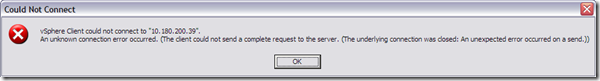
Last week I added some new vSphere 5.5 host in a new configured cluster, the customer is still using Windows XP SP3 32-bit, he received this error message:
An unknown connection error occurred. (The Client could not send a complete request to the server. (The underlying connection was closed: An unexpected error occurred on a send.
Reason:
This issue occurs due to increased security of the cipher strengths which are, by default, used by the VMware Management Web Services components. Due to this change that was introduced in vSphere 5.1, the host operating system is required to support a higher cipher strength to be able to connect to these components.
In Windows Vista and Windows Server 2008, the proper cipher strengths are built into the operating system. However, for older Windows operating systems, a Microsoft hotfix must be applied to add the supported cipher strengths.
For more information on the cipher strengths that get added with the hotfix, see the Microsoft Knowledge Base article 948963.
Solution:
Windows 2003 (32-bit and 64-bit Edition)
For Windows Server 2003 (32-bit and 64-bit), apply the appropriate hotfix to the machine on which the vSphere Client is installed.
Note: If the vSphere Client is installed on the Windows Server where vCenter Server is installed, you must also apply the patch to that Windows Server.
To download the hotfix for your system, see the Microsoft Knowledge Base article 948963.
Notes:
- You must reboot the machine after applying the hotfix.
- Non-English versions of the hotfixes are also available on the Microsoft site. Click the Show hotfixes for all platforms and languageslink on the Hotfix Request page to view the available versions.
Windows XP (32-bit)
There is no hotfix available for Windows XP (32-bit). Microsoft currently only provides limited support for Windows XP, and as a result the hotfix has not been released for it. To resolve this issue, you must upgrade your host operating system to Windows Vista or later, which support the use of high cipher strengths.
If you are unable to upgrade your environment, you may try adding less secure cipher strengths back to the configuration, which allows communication to proceed successfully.
To add less secure cipher strengths back to the configuration:
Caution: This is not a recommended configuration and is provided for backward compatibility purposes only. This is not extensively tested and is supported on a best effort basis only.
- Log in as an administrator to the server where vCenter Server 5.1 is installed.
- Navigate to the tomcat configuration directory.
Note: By default, this directory is located at C:\Program Files\VMware\Infrastructure\tomcat\conf\. In vCenter Server Appliance, the file is located at /ur/lib.vmware-vpx/tomcat/conf. - Open the server.xml file using a text editor.
- Change the Connector text to add support for weaker ciphers by changing it from:
<Connector SSLEnabled="true" acceptCount="100" ciphers="TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA, TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA, TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA, TLS_ECDH_RSA_WITH_AES_256_CBC_SHA, TLS_DHE_RSA_WITH_AES_256_CBC_SHA, TLS_DHE_DSS_WITH_AES_256_CBC_SHA, TLS_DH_RSA_WITH_AES_256_CBC_SHA, TLS_DH_DSS_WITH_AES_256_CBC_SHA, TLS_RSA_WITH_AES_256_CBC_SHA, TLS_DHE_RSA_WITH_AES_128_CBC_SHA,TLS_RSA_WITH_AES_128_CBC_SHA, TLS_DHE_DSS_WITH_AES_128_CBC_SHA, TLS_DH_RSA_WITH_AES_128_CBC_SHA, TLS_DH_DSS_WITH_AES_128_CBC_SHA" connectionTimeout="20000" executor="tomcatThreadPool" keystoreFile="${bio-vmssl.keyFile.name}" keystorePass="${bio-vmssl.SSL.password}" keystoreType="PKCS12" maxKeepAliveRequests="15" port="${bio-vmssl.https.port}" protocol="HTTP/1.1" redirectPort="${bio-vmssl.https.port}" scheme="https" secure="true"></Connector>
To:
<Connector SSLEnabled="true" acceptCount="100" ciphers="TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA, TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA, TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA, TLS_ECDH_RSA_WITH_AES_256_CBC_SHA, TLS_DHE_RSA_WITH_AES_256_CBC_SHA, TLS_DHE_DSS_WITH_AES_256_CBC_SHA, TLS_DH_RSA_WITH_AES_256_CBC_SHA, TLS_DH_DSS_WITH_AES_256_CBC_SHA, TLS_RSA_WITH_AES_256_CBC_SHA, TLS_DHE_RSA_WITH_AES_128_CBC_SHA,TLS_RSA_WITH_AES_128_CBC_SHA, TLS_DHE_DSS_WITH_AES_128_CBC_SHA, TLS_DH_RSA_WITH_AES_128_CBC_SHA, TLS_DH_DSS_WITH_AES_128_CBC_SHA ,SSL_RSA_WITH_RC4_128_MD5, SSL_RSA_WITH_RC4_128_SHA, SSL_RSA_WITH_3DES_EDE_CBC_SHA, SSL_DHE_RSA_WITH_3DES_EDE_CBC_SHA, SSL_DHE_DSS_WITH_3DES_EDE_CBC_SHA" connectionTimeout="20000" executor="tomcatThreadPool" keystoreFile="${bio-vmssl.keyFile.name}" keystorePass="${bio-vmssl.SSL.password}" keystoreType="PKCS12" maxKeepAliveRequests="15" port="${bio-vmssl.https.port}" protocol="HTTP/1.1" redirectPort="${bio-vmssl.https.port}" scheme="https" secure="true"></Connector>
Note: Add only the red text as indicated and do not change any other options. This adds back support for less secure cipher strengths for backward compatibility purposes. - Restart the VMware VirtualCenter Management Web Services service. For more information, see
 Stopping, starting, or restarting vCenter services (1003895).
Stopping, starting, or restarting vCenter services (1003895).
Solution v2.0:
Change the Config on the ESXi5.5-Server
* login to the esxi5.5 via ssh
* modify the following file: /etc/vmware/rhttpproxy/config.xml
* insert the following xml line into the appropriate section:
ALL
* restart the service: /etc/init.d/rhttpproxy restart
*hmpf*
Failed to past Code-Segment, missing Preview-Button.
PLZ Edit:
* modify the following file: /etc/vmware/rhttpproxy/config.xml
<vmacore>
<ssl>
<cipherList>ALL</cipherList>
</ssl>
</vmacore>
Thanks Bigboss! 🙂
@bigboss
Very much appreciated! Works like a charm 🙂
I have the same error in Windows 7. Everything was good until this week, as far as I know nothing has changed on the system (it’s VM just for connecting to ESXi). I checked plenty possible solution on google that could work and nothing… My ESXi is 5 update 1 same as vSphere Client. Have you experienced anything similar?
Did you resolve the issue on windows 7@Wojtek
Yes, I’ve solved my problem quite simply. I haven’t tired this simple method before because I thought “It has to be something serious” 😉 And here is my solution:
1. Log in to SSH or Local console as root.
2. Run these commands:
/etc/init.d/hostd restart
/etc/init.d/vpxa restart
Note: In ESXi 4.x, run this command to restart the vpxa agent:
service vmware-vpxa restart
Solution has been found here: http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=1003490
Good job man! Thx.
Great, good info